Frequently, my day job is inspiration to develop a tool and Access Checker was just that. Though not mine, the great @Tanguy Touzard did the original, I felt that I could update it to include how the user has access.
The original tool allowed you to select a record, select a user and be presented with what access that user had to that record. My enhancement is to present to the user how they gained that access. This was because we have come across a situation where it was unclear how a user got access to a record.
Microsoft has now given us a Check Access button on a record form, but I feel that this is a little clunky, particularly if you want to check multiple records, and the Access Checker also adds, for records that are accessible by inheritance, a link to the record that was shared.
TLDR;
I augmented the Access Checker tool to provide an explanation of how access has been granted.
Walkthrough
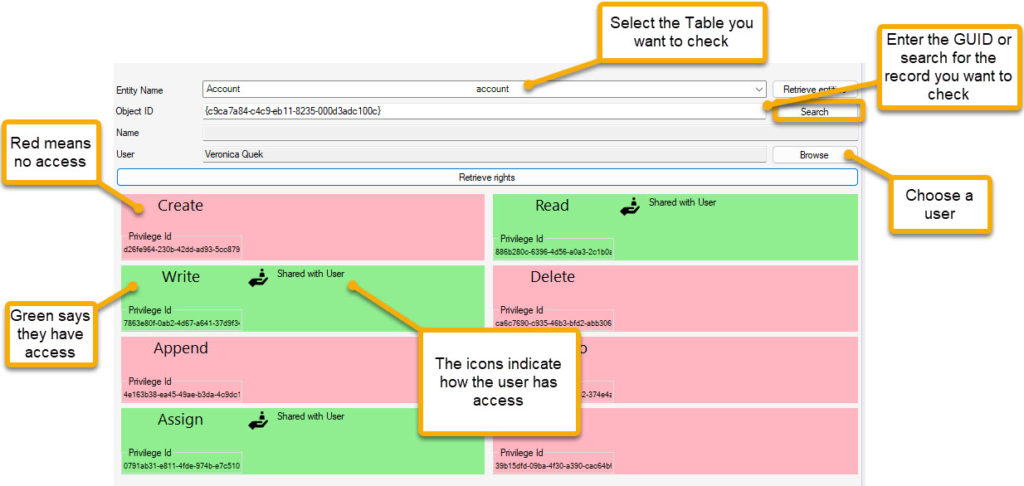
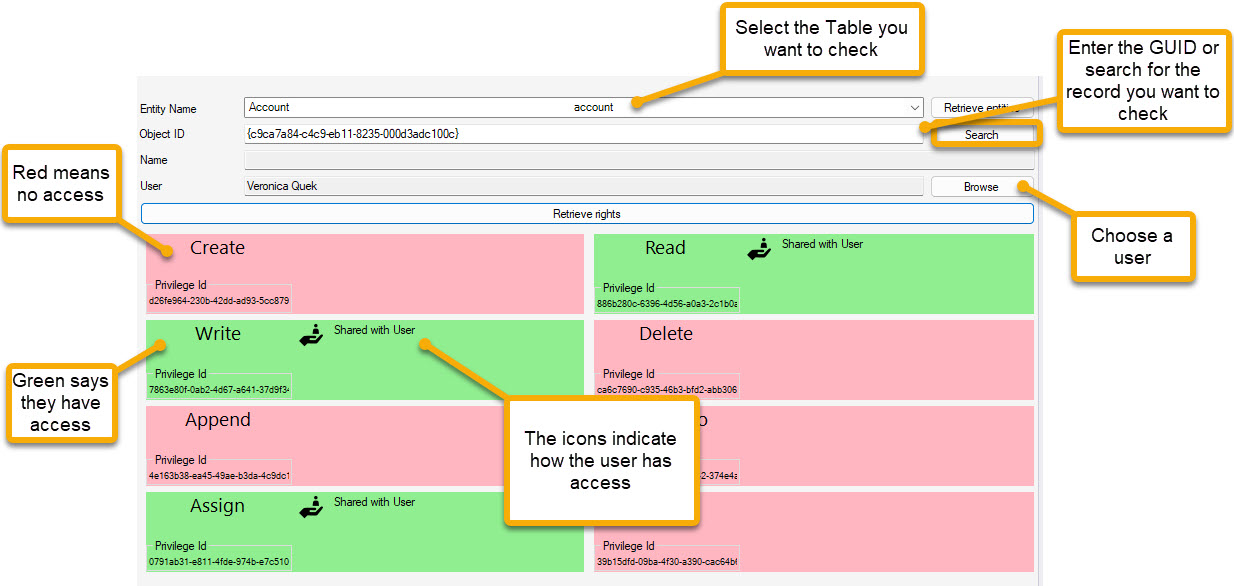
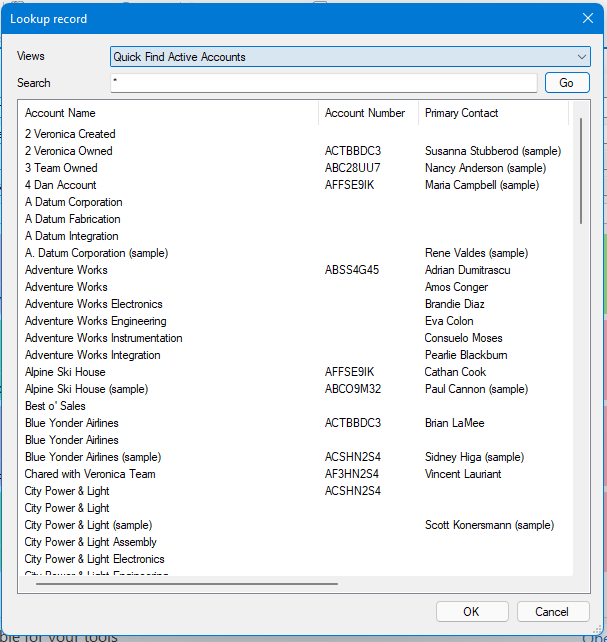
Open the tool and select the Entity (damn, missed the opportunity to change to Table). If you know the record id then just paste it in, otherwise, select the Search button to use a view and find your record.
The Lookup record window allows the selection of a view and searching using * as a wildcard.
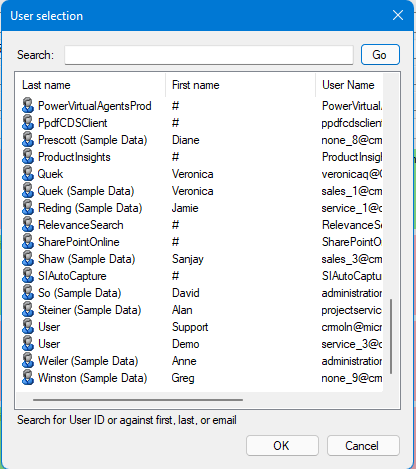
When you have your record, return to the main window and select Browse. The User selection allows a search and selection of a user.
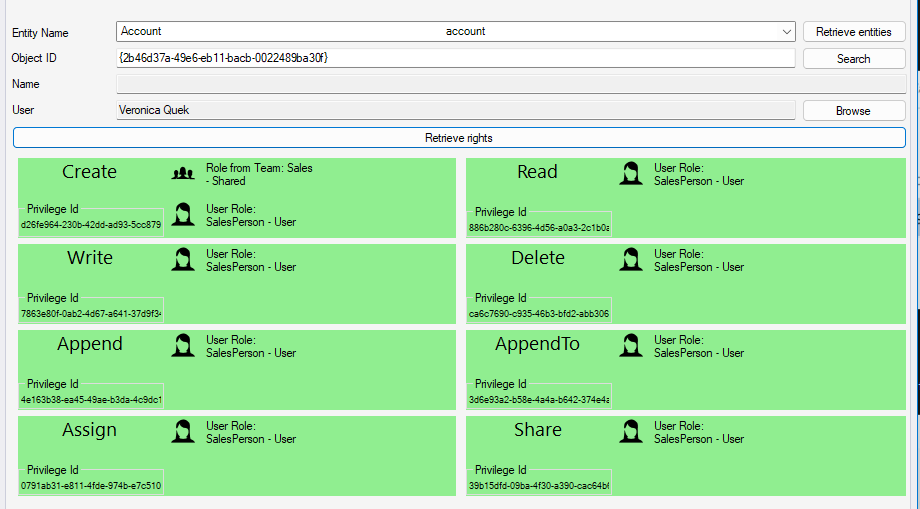
Once done, select Retrieve Rights. The box at the bottom displays a grid showing you the rights that use has to the record. Standard Create, Read, Write, Delete, Append, Append To, Assign and Share derived by the Power Platform security principles.
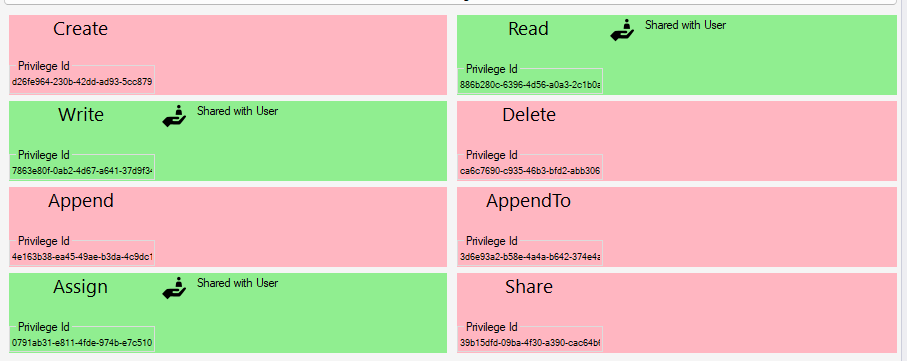
Red means that the user has not got permission to do the action.
Green means they do. Also, there is an icon and words to define how they got access.
The user has the record directly shared with them
The user has access from a share with a related (parent or higher) record.
The user has access due to the role indicated
The user has a role from the team displayed giving them access
Video Walkthrough
Please let me know what you think & log an enhancement/issue on GitHub here.